
Summary
REALLY’s PrivateCore™ is our built-in software layer that sits between you and the cell phone towers. Combining anonymous signup with other technology, it protects your privacy. Think “VPN for the telecom stack,” but broader.
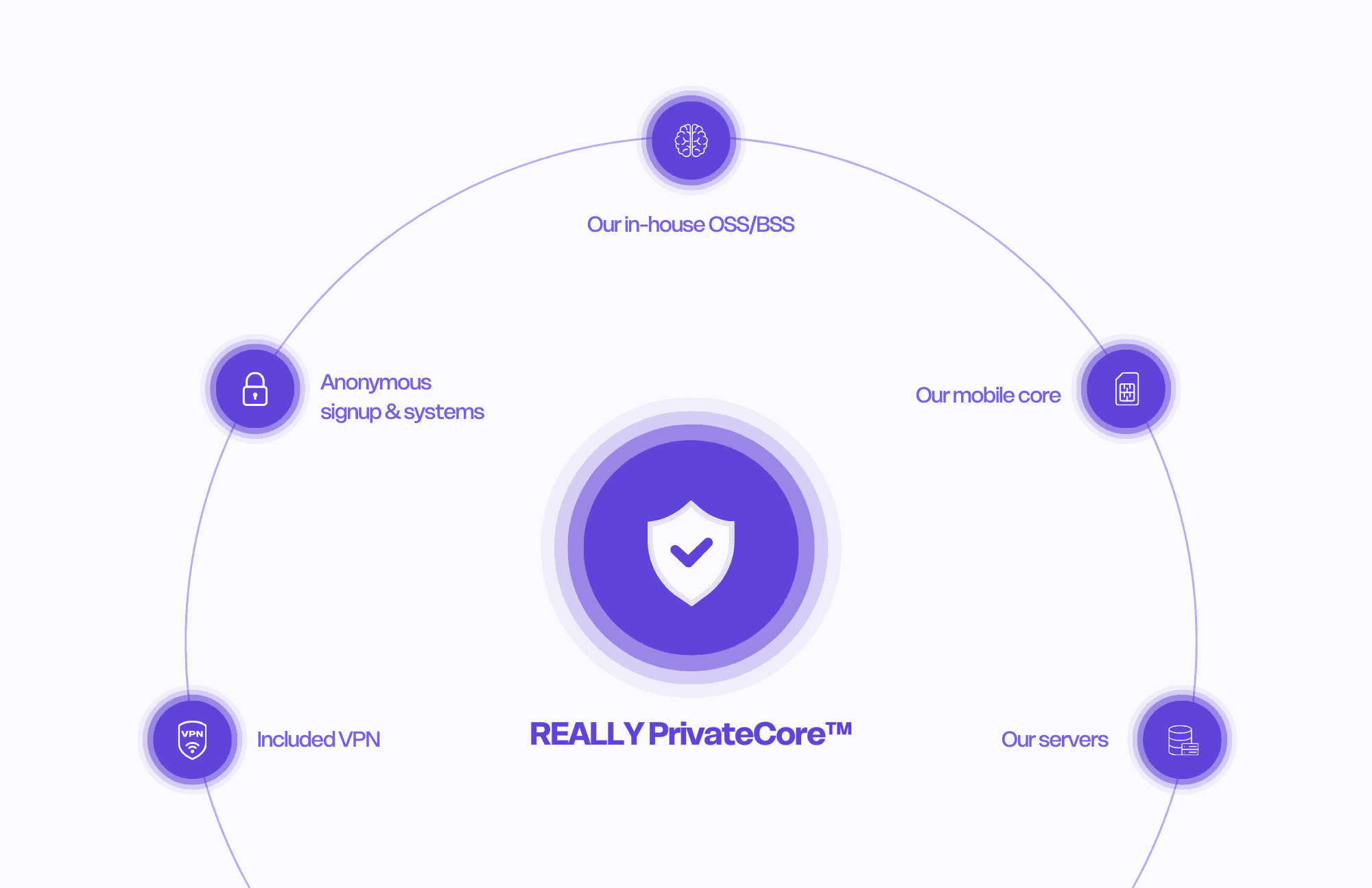
What makes PrivateCore™ unique is the combination of anonymous signup & systems, our in-house OSS/BSS (the brain), our mobile core (the real-time engine used for DeWi), servers we operate (critical control off public cloud), and an included VPN for your device’s internet traffic.
We don’t collect PII, don’t maintain a centralized, identity-linked archive, and don’t monetize customer data. Operational records are minimal and short-lived. Unlike almost every other carrier, there is no dossier on you that includes your personally identifiable information.
Result: mass surveillance doesn’t work here. Targeted, court-supervised requests can still proceed across relevant parties creating a due-process puzzle, but its not a bulk dump and there is ZERO data monetization.
The critic’s question
“Is ‘PrivateCore™’ just branding, or does it actually change my privacy and reliability versus big wireless?”
What is PrivateCore™ (In Plain English)
PrivateCore™ is the software layer that runs our cell phone service, enables your privacy, and makes everything work together, designed so it can’t become an identity-linked dossier by shielding information from cell towers and roaming partners.
Anonymous signup & systems
We activate, operate, bill, and support your line using anonymous signup & systems that avoid PII (Personally Identifiable Information) collection, keep records minimal and short-lived, and prevent any centralized, identity-linked archive.Our in-house OSS/BSS (the brain)
Provisioning, number operations, billing/charging, support, assurance; built and run by us.No centralized, identity-linked archive
Short, purpose-bound retention with enforced ceilings
No data monetization
Our mobile core (the real-time engine)
Authenticates SIM/eSIM, applies live policy/QoS, routes voice/SMS/data, manages mobility/handovers.Tuned for modern call paths (e.g., VoLTE/VoNR where available)
Powers DeWi coverage deployments
Our servers (critical control off public cloud)
Core control planes run on infrastructure we operate, reducing third-party exposure and broad cloud threat surfaces.Segmentation, hardening, and automated purge enforce short retention
Included VPN (device data path)
Encrypts your device’s internet traffic and masks IP on untrusted networks.Complements PrivateCore; it’s not a replacement for a private-by-design carrier stack
“VPN for telecom”
A VPN prevents easy profiling of your internet traffic. PrivateCore™ applies that spirit to the carrier stack: we minimize what’s collected, compartmentalize what exists, and avoid any centralized, identity-linked archive.
How PrivateCore™ protects privacy
No PII collected
No subscriber-identity mapping kept and no centralized, identity-linked archive
Short-lived operational records with published ceilings and automated deletion
Strict interface controls (field whitelists, minimal exports)
No data monetization
Due-process only: targeted, court-supervised requests proceed across multiple parties, not a one-stop bulk handover
Reliability you can feel
Real-time core keeps calls, texts, and data stable; smooth mobility/handovers
Assurance without identity leakage: we observe quality and fix issues without building long-term identity-linked histories
DeWi expansion improves coverage in hard places; architecture is multi-bearer-ready (e.g., satellite integrations over time)
Practical scenarios
Everyday calling/texting: Works normally. Under the hood, PrivateCore runs policy and routing without creating an identity-linked archive.
On hotel/airport Wi-Fi: Enable the included VPN to encrypt your device’s internet traffic; PrivateCore continues to protect the carrier side.
Sensitive conversations: Keep calls on modern legs (we prioritize them). For content confidentiality, use an end-to-end encrypted app; the VPN helps protect that data path, too.
Legal & compliance (In Plain English)
We believe in privacy and freedom. We’re engineered to block mass surveillance, not to shield individual criminals. In the U.S., we comply with CALEA, E911, CPNI rules (47 U.S.C. §222), and applicable parts of ECPA (Stored Communications Act; Pen Register/Trap & Trace; Wiretap Act), FISA where applicable, and relevant state laws. Targeted access (warrants, court orders, subpoenas) follows due process across multiple parties, we simply don’t run a centralized, identity-linked archive to hand over in bulk.
Honest limits
PSTN isn’t end-to-end encrypted. We harden defaults (prefer modern legs where available) and recommend end-to-end encrypted apps for sensitive content.
Emergency services (E911) require specific information flows; we meet legal obligations while keeping long-term archives off the table.
Compromised devices can still leak; pair PrivateCore with device-level hygiene and the included VPN on risky networks.
Proof & verification (in progress)
Coming soon:
Architecture & data-flow diagrams showing which fields never cross boundaries and where encryption applies
Retention Matrix with concrete TTLs per table/topic + automated deletion test logs
Interface inventory proving no centralized, identity-linked archive exists and exports are minimal
Voice-path captures for modern legs (where available)
Transparency counters (received/complied/narrowed/rejected lawful requests)
Independent reviews/attestations aligned to the above
Join the only carrier that makes privacy non-negotiable.




