
Summary
REALLY uses the same towers, but different software . T-Mobile provides a RAN (cell towers), but REALLY built a software layer called the REALLY PrivateCore™ that runs the “brains” improving subscriber's privacy and shielding personal information so networks like T-Mobile or other roaming partners don’t receive any identifier mapping. Most of the important or sensitive stuff happens at this software layer.
There is no one-stop archive like there would be at almost every other cellular provider REALLY doesn’t keep a centralized, identity-linked dossier. What exists is minimal, siloed, and short-lived.
Cell tower records ≠ your account. Host towers generate technical events (CDRs), but those aren’t tied to your REALLY account through us, and we don’t warehouse them for years like Big Wireless.
Result: You get nationwide coverage without handing hosts your identity-linked usage history. Lawful, case-specific access still works via due-process requests across relevant parties.
The Critic’s Question
“If you ride on T-Mobile’s towers, how can you claim privacy? Don’t they see everything?”
Why This Works (In Plain English)
Think of a cell network as two parts:
RAN (Radio Access Network) = the cell towers, move radio signals to/from phones.
The B/OSS, part of our PrivateCore™, (the “brains”) + a Mobile Core, which together authenticate subscribers, route traffic, bill, support, and log.
Most MVNOs lean on the host’s ‘brains’ (or pump data into them), which exposes identity-linked activity by default. REALLY is different: we run our own core and B/OSS, keeping subscriber identity mapping and operational records in our systems, not the host’s.

What the Host Sees vs. What We Keep
At the Host (T-Mobile cell towers)
Technical radio events (CDRs): time, serving cell, technical identifiers needed to run radio service.
No mapping from us: they don’t receive any account or network identifier mapping (e.g., IMSI/eSIM/ICCID ↔ account).
No access to our B/OSS records (billing, care, support notes).
Inside REALLY (PrivateCore™)
No subscriber mapping (the minimum link required to operate service), kept siloed with short retention and least-privilege access.
No centralized, identity-linked archive of historical usage.
No monetization of customer data.

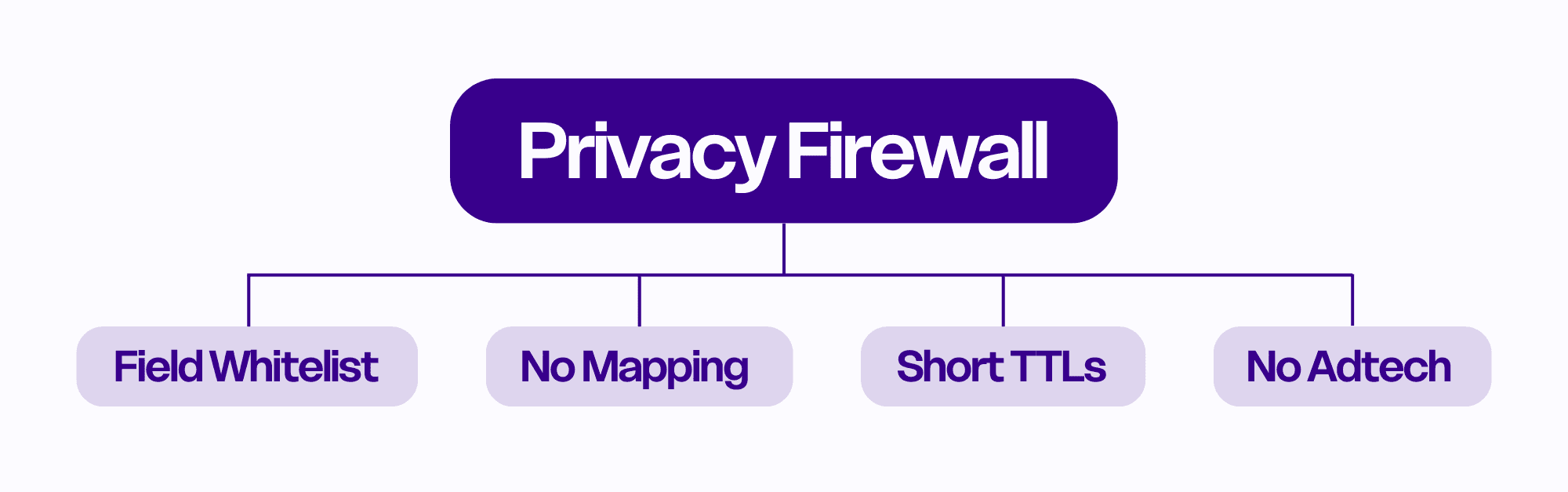
The “Privacy Firewall”
Our architecture draws a hard line between radio events and identity:
Field whitelists: Only strictly necessary technical fields cross between parties.
No identifier mapping shared: The join between tower events and a named subscriber doesn't exist.
Short retention + silos: What we keep for operations is time-bounded and segmented to reduce blast radius.
No adtech pipes: We do not feed data to advertising or broker systems, because we don't have it.
What About CDRs?
CDR = Call Detail Record (metadata about an event, time, cell, duration, technical IDs, not call content).
Hosts necessarily create CDRs to run a radio network.
Key difference with REALLY: those tower CDRs are not tied to your account through us, and we don’t warehouse identity-linked histories.
How Lawful Requests Work (No Dragnets)
Targeted, court-supervised requests go to the relevant parties:
Host (towers): tower-level technical events (CDRs).
REALLY: only the minimal, short-lived records that actually exist.
Apps/clouds, banks, device forensics: their scoped records.
No single bulk dump: It’s a due-process puzzle, not mass collection (see Explainer #3).
Big Wireless vs. REALLY (Side-by-Side: Data Layer)
Topic | Big Wireless (typical) | REALLY |
|---|---|---|
Core + B/OSS location | Host carrier | REALLY-owned |
Identifier mapping at host | Often present | Does not exist |
Identity-linked archives | Centralized, long-retained | No one-stop archive |
Monetization | Common | None |
Retention | Multi-year by default | Short, purpose-bound TTLs |
FAQs
Do you sell or share my data?
No. We don’t monetize customer data.
Can the host tie tower logs to me anyway?
Not through us. We don’t send any account identifier mapping to hosts, because we don't have it.
If there’s an investigation, does this block access?
No. It ensures targeted, lawful access across the relevant parties instead of a bulk dump (see #3).
Why not just build your own towers?
We are building DeWi coverage over time, meanwhile, using nationwide towers without handing over identity mapping gives you privacy now.
Wrap-Up
Using T-Mobile’s towers does not mean handing them your identity-linked usage history. REALLY runs the brains, keeps mapping in-house, doesn’t centralize archives, and limits retention, so you get coverage without the surveillance substrate.
Same towers. Different defaults.
Join the only carrier that makes privacy non-negotiable.




